The Web Browser Padlock: What It Means and Why It Might Soon Disappear.

The little padlock on a web browser’s address bar has become a familiar and reassuring sign of security. It used to appear only when sensitive information was to be submitted. Now it’s almost everywhere. Why? And why might it soon disappear?
What the Padlock Means. It indicates that a connection uses the secure HTTPS protocol and, therefore, that:
- The connection is with the requested server,
- Communication with that server is encrypted so only the sender and recipient can read it, and
- Unauthorized content cannot be inserted by third parties.
Why Is This Important? The Internet was not designed with security in mind — it was intended as a vehicle for academicians and researchers to share data and findings. Ordinary internet communications are as open as messages written on a postcard. No one would send credit card information that way. People sending sensitive information want to know (1) that it can only be read by the intended recipient, (2) that it will be delivered only to that party, and (3) that it can’t be altered en route. HTTPS provides these assurances and the padlock indicates when it is being used.
How Does Encryption Work? Anyone handling a post card can read what’s on it, but if a message is written in a secret code, only those who know the code will understand it. Children sometimes send secret messages to friends this way. For example, members of their group might say “see you at lunch” when they mean “let’s go out tonight.” The message can be shouted across a room, but only insiders know the hidden meaning. Computers encode with complex digital manipulations, not simple phrase substitution, but the idea is exactly the same.
This kind of encryption works for internal communications since an organization can install the “private key” needed to encode and decode messages on each employee’s computer. But it won’t work for on-line commerce since a merchant needs to be able to communicate privately with customers who won’t have the its “private key.”
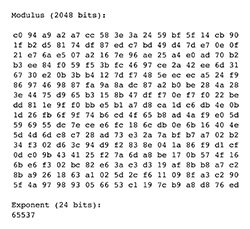
The solution is “public key” encryption. The merchant combines two large numbers, which it keeps secret, to generate a third, much larger number, which it posts on its web server as its “public key.” Anyone can use the public key to encrypt data sent to the merchant, but only the merchant’s secret private keys can decipher them.
The problem is that the public key numbers are so large that encoding messages with them takes a long time. So once secure public key communication has been established, it is used to transmit a much smaller “private key” that both computers then use for the remainder of the session.
Theoretically, a hacker could keep guessing different private keys until it found the one that worked. But public key numbers are so huge that even the fastest supercomputers would take so many years to try all the possible combinations2 that the encrypted information would likely have become obsolete long before the code was broken.3
How Does HTTPS Help Ensure Connection to the Proper Party? Encryption protects messages in transit, but won’t help if a connection has been hijacked since the hijacker’s server will be able to decipher messages created with its own public key. Such hijacking typically involves a hacker substituting its server’s IP address for that of a legitimate site.
An IP address is a unique string of numbers assigned to an internet-connected device. For example 208.71.139.20 is the IP address for www.computerimages.com. Most people, however, navigate the web using easy to remember domain names like www.computerimages.com, not IP addresses. DNS servers look up the IP addresses for those domain names and it is during this process that hijacking can occur.
HTTPS helps protect against this by requiring that a server’s IP address match that in a Server Certificate issued by trusted Certificate Authority.5 The Server Certificate ties the domain name to a specific IP address. If a connection is hijacked to a different IP address, an HTTPS connection cannot be established.
HTTPS Prevents Messages from Being Altered. In 2016, the FTC fined Verizon for injecting tracking headers into mobile customers’ web traffic even where customers had turned on Android or iOS do not track settings. The headers were part of Verizon’s Precision Market Insights program. The NSA and Britain’s GCHQ used content injection to take over a Belgian ISP’s computers. HTTPS connections cannot be compromised in this way.
Why HTTPS Is Becoming the Norm. As the Internet permeates our daily activities, it becomes increasingly attractive to evildoers. Every day’s news brings another story of fraud, leaks, threats to the power grid and now manipulation of elections. Network protection is critical since security is only as strong as the weakest link.
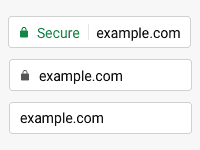
To meet the challenge, computer security organizations, advocacy groups like the Electronic Frontier Foundation and frontline companies like Google have been pushing to make HTTPS easier and less costly to implement with the goal of making it universal. Peer pressure is also being applied with the latest version of Google Chrome now identifying non-HTTPS sites as “Not Secure.”
Why the Padlock Might Soon Disappear. If everyone wants HTTPS, why might the familiar padlock disappear? The answer is Google wants HTTPS pages to be considered the norm so some future version of Chrome will no longer use the padlock to mark them as special. Instead, a prominent “Not Secure” warning will be displayed for all non-HTTPS pages. Other browsers, of course, may not follow suit.
* * * * *
The disappearance of familiar icons often creates concern and confusion. Hopefully Google is working on a good plan for convincing Chrome users that their connections are still safe even when they no longer see the familiar padlock.
-----
- The two-character entries are hexadecimal numbers. The lowest value, 00, equals 0; the highest, ff, equals 255, and there are 254 combinations in between. People who create web sites might recognize hexadecimal numbers from their use in specifying RGB colors in HTML and CSS.
- There are 22048 possible combinations. It’s the same as flipping a coin 2048 times.
- Mia Epner gives a good explanation of public key encryption in an on-line video, Encryption and Public Keys, at Khan Academy.
- Image adapted from graphic at Emily Schechter, Evolving Chrome’s Security Indicators, Chromium Blog (May 17, 2018).
- Actually it is the user’s web browser that requires the Server Certificate to be issued by a trusted Certificate Authority. An organization can create its own self-certified Server Certificate and use it for internal HTTPS communication, but no major web browser would recognize it as safe.
- Schechter, op. cit.
This article originally appeared in our free semi-monthly newsletter. To receive future issues, please add your name to the subscription list.

